When You Fall Victim To A Cyber-Attack Through
No Fault Of Your Own, Will They Call You
Stupid... Or Just Irresponsible?
It's EXTREMELY unfair, isn’t it? Victims of all other crimes – burglary, rape, mugging, carjacking, theft – get sympathy from others. They are called “victims” and support comes flooding in.
But if your business is the victim of a cybercrime attack where client or patient data is compromised, you will NOT get such sympathy. You will be instantly labeled as stupid or irresponsible. You will be investigated and questioned about what you did to prevent this from happening – and if the answer is not adequate, you can be found liable, facing serious fines and lawsuits EVEN IF you trusted an outsourced IT support company to protect you. Claiming ignorance is not an acceptable defense, and this giant, expensive and reputation-destroying nightmare will land squarely on YOUR shoulders.
Don't believe me? Check out this February, 2017 article:
Data Breaches on the Rise – Customers are Blaming Breached Companies
 When it comes to network security, it is easy for small to medium sized businesses to say “not me”, “they are only after the big guys.” The reality is that attacks on all networks have been increasing year after year as hackers have become more sophisticated, and small businesses are being affected every day by relaxed or non-existent security policies.
When it comes to network security, it is easy for small to medium sized businesses to say “not me”, “they are only after the big guys.” The reality is that attacks on all networks have been increasing year after year as hackers have become more sophisticated, and small businesses are being affected every day by relaxed or non-existent security policies.
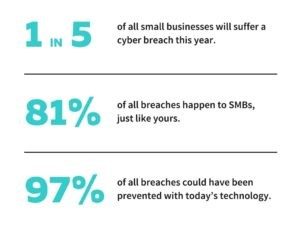
A 2013 study showed that 1 in every 5 small businesses networks would be compromised. With the ever-increasing technological advances, it is likely that since then, these numbers have climbed, posing a significant risk for a potential breach, lost or stolen data, or some type of malicious threat.
There are a number of ways Houston based Momentum IT helps to layer protection to minimize your risk:
- Updates- Keeping computers and network equipment updated is one of the most effective steps to preventing a possible network security issue.
- Firewall- A common mistake in small to medium business networks is the lack of a business grade firewall solution. Often business owners are unaware of the difference between having a network router and having a network firewall in place. This is the front door to global threats and as your front door, it's even more critical updates are monitored & applied regularly. Don't leave it unlocked & un-monitored.
- Passwords- Password and password protection are proving to be an area that needs attention when discussing network security. Using sophisticated software and tools, hackers are easily gaining access to small business networks through simple or default passwords. We protect you with enterprise level password managers you can provide to your employees as an employment benefit.
 Advanced Endpoint Protection/Antivirus/Antispam- Most people know that antivirus and antispam software are necessary components of network security, but many people don’t realize why its so important until their computer or network is infected with a virus, malware, spyware, or a host of other potentially dangerous issues. Our protection was previously only available to Fortune 500 companies. Now we are offering that protection to you, "the little guy" so you don't need to lay awake at night worrying about cyber criminals.
Advanced Endpoint Protection/Antivirus/Antispam- Most people know that antivirus and antispam software are necessary components of network security, but many people don’t realize why its so important until their computer or network is infected with a virus, malware, spyware, or a host of other potentially dangerous issues. Our protection was previously only available to Fortune 500 companies. Now we are offering that protection to you, "the little guy" so you don't need to lay awake at night worrying about cyber criminals.- Cyber Security Training For You And Your Employees- One careless click can bypass much of the protection offered today. The best approach is to train your employees, as well as yourself, regularly and that's included with our Guardian Angel Security Training. This isn't a one time and done type of training. That type of budget spend is virtually worthless. This is year-round cybersecurity awareness that includes crucial follow up such as sample phishing emails to all your employees (including YOU) with reinforcement education should they not recognize the risk. Although there's no silver bullet when it comes to cyber security, this is as close as you're going to get for the cost. You may even be eligible for a discount on your cyber insurance premiums. Ask your insurance agent.
Dark Web Monitoring For Corporate Stolen Passwords - Access to your business is for sale by criminals on a hidden part of the Internet called "The Dark Web." These are the dark alleys where cyber thugs and criminal states buy and trade data stolen with each breach you hear in the media. They steal your username & password from companies such as DropBox, LinkedIn, Netflix, and the list goes on. You need an early warning system to alert you when this happens so additional protective measures can be taken to keep you from being one of those breached companies in the news. All the technology in the world won't stop a criminal with valid credentials logging into your network.
No matter the size of your business, network security is a definite requirement for every business in the digital age. If you are worried or unsure of where to start with an internal security audit, our team can help get you on track and within your budget.
"But I Have An IT Guy." You Say
When it comes to protecting your company, you need to know for certain – without any lingering doubts – that you are doing everything you can to avoid being an easy target for cyber criminals. In my admittedly informal survey, talking to over dozens of CEOs who have been hacked or compromised, almost all of them told me they thought their IT guy “had things covered.”
Not a single client has been impacted by ransomware or any other malware while under our Security Plus program. We can't guarantee it won't happen, but we'll give you the best protection available for your budget dollar.
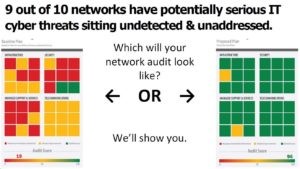
That's why we provide an extensive audit of your network vulnerability. The report can run up to 600 pages of detail, but we include an easy to read summary and actionable plan to get you covered. We also sit down with and go over the summary with you. Speaking of covered, it's covered by our 100% satisfaction guarantee. You can't lose, unless you choose to do nothing.
FREE REPORT
The Top 10 Ways Hackers Get Around Your Firewall and Anti-Virus to Rob You Blind


